SCIM integration with an Identity Provider: Manual/Custom approach
This topic discusses integrating the product with an Identify Provider (IdP), using your own code to integrate the IdP with the product via SCIM. This approach may be required when there is no specific app or extension available for the SCIM 2.0-compatible IdP that you want to integrate with, or if you want to build your own custom app or service to synchronize identities from your IdP with the product, perhaps because your organization requires only certain identities to be synchronized with the product via SCIM.
OAuth Refresh token expiry
Standard OAuth operation is that your access token expires in a given time, usually 60 minutes, and your refresh token allows you to get a new access token. By default, the refresh token expires every 30 days. If you have a custom SCIM implementation, like described in this topic, it stops working when the refresh token expires and you get an error message.
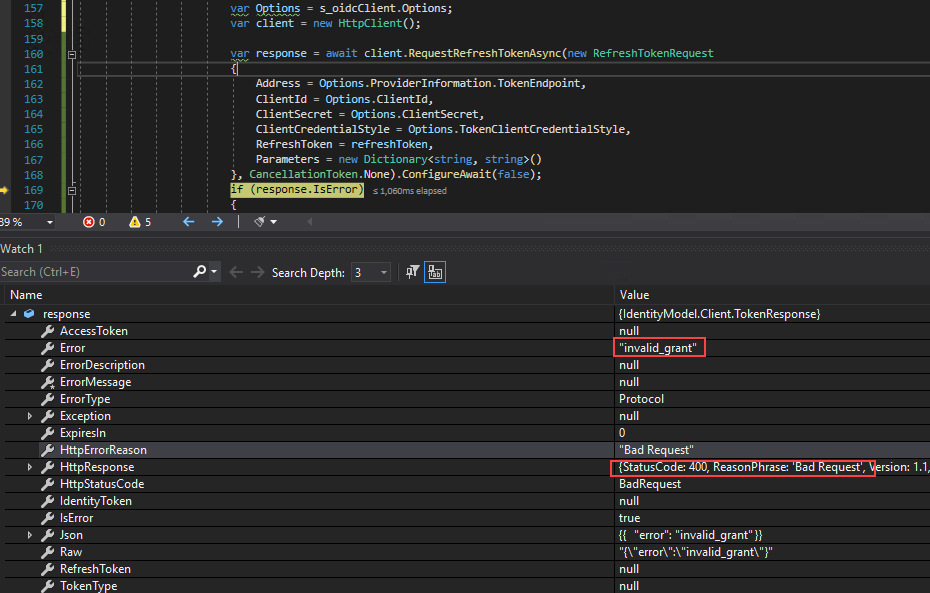
Here you can see an HTTP response 400, Bad Request with the invalid_grant message when you call the RequestRefreshTokenAsync directly from an HttpClient: